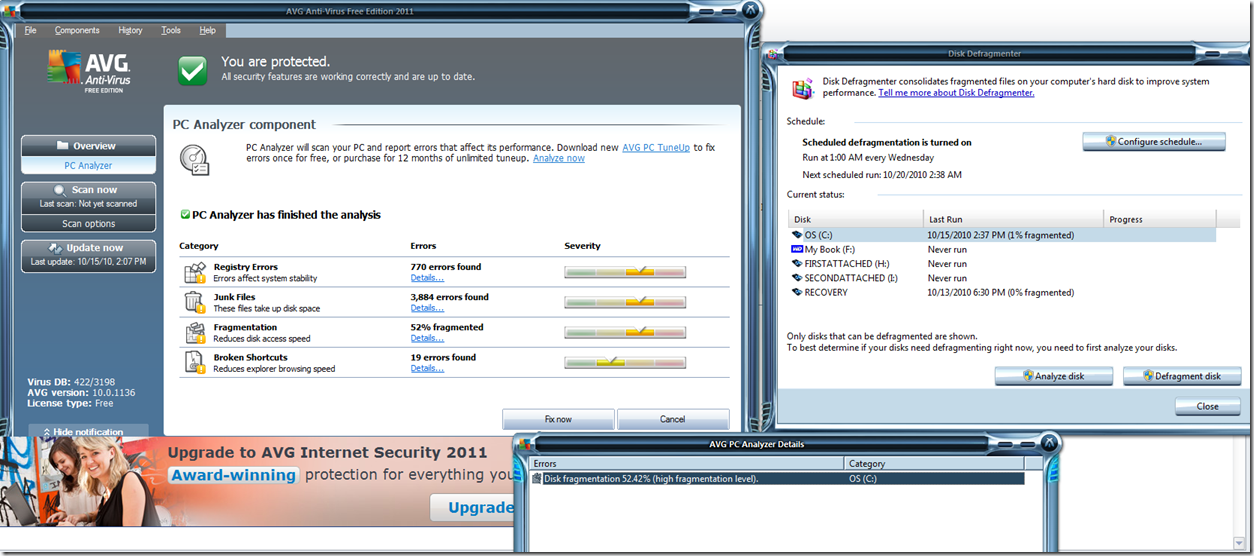
This afternoon I updated to AVG Free 2011, and a short while later, I was presented with this popup to scan my system with the PC Analyzer. I figured, what the heck. When the scanning was complete, I noticed that it said my hard drive was 52% fragmented… and if I wanted to fix it “once” i could do so for free, or buy a 12 month subscription.
Well, being the savvy user that I am (and also concerned at how my hard drive could become so fragmented) – I grabbed windows Disk Defragmenter tool and checked my hard drive. Windows reports that I’m 1% fragmented, and AVG reports that I’m 52% fragmented.
Now, AVG has always seemed to be an excellent tool, and I have recently stopped using Trend Micro and Norton (both of which I used to pay for) for the simple and seemingly solid protection of AVG.
However, I have to ask – is their Fragmentation engine just that buggy, or are they being dishonest and unethical by representing a level of PC Problems that do not actually exist, thinking that most users will just run out and buy their additional software…
Either way, I wasn’t so impressed with AVG’s PC Analyzer Product.